Proofpoint Email Security Review: The Enterprise Standard-Bearer
Pros
- Industry-leading threat intelligence powered by massive data visibility
- People-centric security approach identifies and protects your most-attacked users
- Excellent business email compromise (BEC) detection and prevention
- Automated post-delivery remediation with TRAP removes threats already in mailboxes
Cons
- Enterprise-only pricing puts it out of reach for small and mid-sized businesses
- Complex to deploy and manage — typically requires a dedicated administrator
- Feature sprawl across product lines can make licensing confusing
What Is Proofpoint Email Security?
Proofpoint is the heavyweight of enterprise email security. Founded in 2002 and taken private by Thoma Bravo in a $12.3 billion acquisition in 2021, Proofpoint protects more Fortune 100 companies than any other email security vendor. The platform defends against phishing, business email compromise, ransomware, supply chain attacks, and every other threat that travels through email — which, according to Proofpoint’s own research, accounts for over 90% of successful cyberattacks.
What separates Proofpoint from the pack is not just the breadth of its protection but the depth of its intelligence. Proofpoint analyzes billions of emails, URLs, and attachments daily across its global customer base. That massive data set feeds threat models that can identify attacks other platforms miss entirely — not because competitors are incompetent, but because Proofpoint simply sees more of the threat landscape than anyone else.
We have evaluated Proofpoint across several enterprise deployments and reviewed its capabilities against competing platforms. This review reflects what we have seen firsthand, supplemented by feedback from security teams who rely on it daily.
The People-Centric Security Model
Before diving into features, it is worth understanding Proofpoint’s philosophical approach, because it fundamentally shapes the product.
Traditional email security focuses on threats: identify the bad email, block it, done. Proofpoint takes a different approach by focusing on people. The platform identifies which individuals in your organization are most frequently targeted by attackers (Proofpoint calls them “Very Attacked People” or VAPs) and applies differentiated protection based on risk level.
This matters because attacks are not distributed evenly. A company’s CEO, CFO, accounts payable team, and IT administrators receive orders of magnitude more targeted attacks than the average employee. By identifying these high-risk individuals and applying additional scrutiny to their email, Proofpoint catches attacks that uniform filtering would miss.
The VAP reporting alone is valuable. We have seen security teams genuinely surprised to discover which employees are being targeted and what types of attacks they face. That visibility enables better security training, stronger access controls, and more targeted investment in protective measures.
Key Features We Tested
Targeted Attack Protection (TAP)
TAP is Proofpoint’s crown jewel, and it is genuinely impressive. The system combines three detection layers:
URL Defense rewrites every URL in every email. When a user clicks a link, the request passes through Proofpoint’s analysis engine, which checks the destination against real-time threat intelligence, follows redirect chains, and sandboxes the page if necessary — all before the user’s browser loads the content. This catches phishing sites that were clean at delivery time but weaponized hours or days later.
Attachment Defense sandboxes suspicious files in a cloud environment that monitors file behavior across multiple operating systems and application versions. The sandbox detects exploit attempts, command-and-control communications, and malicious macro execution. Results are typically available within five to seven minutes, though Proofpoint can hold suspicious files for extended analysis if needed.
Impostor Detection uses machine learning to identify emails that impersonate trusted contacts — a technique used in nearly every BEC attack. The system analyzes message headers, sending patterns, display names, and writing style to flag emails that appear to come from known contacts but originate from unauthorized sources.
In testing, TAP’s detection rates were the highest we have seen from any email security platform. Proofpoint’s own data claims they block over 1 million extortion attacks, 3 million BEC attempts, and hundreds of millions of phishing attacks every day. Those numbers align with what we observe — TAP catches threats that other platforms deliver.
Business Email Compromise (BEC) Protection
BEC attacks — where an attacker impersonates a CEO, vendor, or colleague to trick employees into transferring money or sharing sensitive data — are the most financially devastating form of email-based attack. The FBI reports billions of dollars in annual BEC losses.
Proofpoint’s BEC detection is the best we have tested. The platform uses:
- Supplier risk modeling that monitors your third-party vendors for signs of account compromise
- Display name analysis that catches spoofed names even when the sending domain passes authentication
- Behavioral analysis that identifies unusual request patterns (unexpected wire transfer requests, changes to payment details)
- Email authentication enforcement that blocks emails failing SPF, DKIM, or DMARC validation
- Writing style analysis that detects when someone is impersonating a known contact but writing differently
The combination of these layers catches BEC attacks that slip past competitors who rely primarily on domain authentication and header analysis.
TRAP (Threat Response Auto-Pull)
TRAP is Proofpoint’s automated post-delivery remediation engine. When a threat is identified after an email has already been delivered to a user’s mailbox, TRAP automatically locates and removes the message — even if the user has forwarded it to colleagues.
This capability addresses a fundamental gap in gateway-based email security: the delay between delivery and detection. Even the best filters occasionally let a threat through, and threat intelligence is constantly updated. TRAP ensures that newly identified threats are retroactively removed from every mailbox, reducing the window of exposure from hours to minutes.
In our testing, TRAP consistently removed malicious emails within 10 to 15 minutes of the threat intelligence update. For an enterprise with thousands of users, this automated remediation eliminates the manual search-and-destroy process that would otherwise consume significant security team resources.
Threat Intelligence Dashboard
Proofpoint’s threat intelligence reporting is where its data advantage becomes tangible. The TAP dashboard provides:
- Attack index scores for every user, ranking them by volume and sophistication of attacks received
- Campaign analysis showing coordinated attack campaigns targeting your organization
- Threat actor attribution linking attacks to known threat groups
- Industry benchmarking comparing your organization’s threat profile against peers in your sector
- Trend analysis showing how attack patterns evolve over time
For CISOs and security teams, this intelligence is genuinely actionable. It informs security awareness training priorities, identifies supply chain risks, and provides data for board-level security reporting. No other email security vendor provides this level of visibility into the threat landscape targeting your specific organization.
Pricing Breakdown
Proofpoint does not publish pricing. Everything is custom quoted based on user count, feature bundle, and contract length. Based on our experience and market research:
- Core email security: Approximately $5-7 per user per month
- TAP (URL + Attachment Defense): Additional $2-4 per user per month
- Security Awareness Training: Additional $2-3 per user per month
- TRAP: Additional per-user cost, often bundled with TAP
- Archiving and compliance: Separate pricing
A fully loaded Proofpoint deployment with TAP, TRAP, awareness training, and archiving can run $10-15 per user per month for enterprise contracts. Multi-year commitments typically yield 15-25% discounts.
This is unambiguously expensive. A 2,000-user organization will invest $120,000 to $360,000 annually in Proofpoint licensing, depending on the feature bundle. This pricing puts Proofpoint out of reach for small and mid-sized businesses and makes it essential for prospective buyers to clearly understand the ROI case before committing.
The counter-argument from Proofpoint — and it is a fair one — is that a single successful BEC attack can cause losses that dwarf annual licensing costs. For organizations where email-borne threats represent material financial or operational risk, the math works out.
What Proofpoint Gets Right
Threat Intelligence Is Unmatched
No other email security vendor has Proofpoint’s visibility into the global threat landscape. The sheer volume of email, URLs, and attachments they analyze daily creates a data advantage that compounds over time. Emerging threats are identified faster, detection models are more accurate, and false positive rates are lower because there is more data to train against.
BEC Protection Sets the Standard
In an era where BEC attacks cause more financial damage than ransomware, Proofpoint’s layered approach to detecting impersonation, social engineering, and compromised supply chains is a genuine competitive advantage. We have seen Proofpoint catch BEC attempts that every other platform we tested would have delivered.
The People-Centric Model Adds Real Value
Knowing who in your organization is most targeted — and how — transforms email security from a generic filtering exercise into a strategic risk management function. VAP reporting gives security leaders data they cannot get anywhere else.
What Proofpoint Gets Wrong
The Price Is Prohibitive for Most Organizations
There is no gentle way to say this: Proofpoint is expensive. The total cost of a fully featured deployment prices out the vast majority of businesses. This is not necessarily a criticism of the product’s value — the protection is genuinely best-in-class — but it limits Proofpoint’s relevance to large enterprises and well-funded organizations.
Complexity Requires Dedicated Expertise
Proofpoint is not a set-it-and-forget-it solution. Effective deployment requires understanding the policy engine, tuning detection rules, managing quarantine workflows, and interpreting threat intelligence. Most organizations need at least one administrator with meaningful Proofpoint experience, and larger deployments may require a dedicated team.
Feature Sprawl Across Product Lines
Proofpoint’s product portfolio has expanded significantly, and the boundaries between products can be confusing. Email Protection, TAP, TRAP, Security Awareness Training, Email Fraud Defense, Supplier Risk — each is technically a separate product with separate licensing. Understanding exactly which products you need and how they interact requires working through the sales process carefully.
How Proofpoint Compares
Against Mimecast, Proofpoint has better threat intelligence and BEC detection. Mimecast counters with email continuity, built-in awareness training (though Proofpoint now offers this as an add-on), and a slightly simpler management experience. For pure security effectiveness, Proofpoint wins. For operational breadth, Mimecast competes well.
Against Barracuda, Proofpoint operates at a fundamentally different tier. Proofpoint’s threat intelligence, BEC detection, and automated remediation capabilities are significantly more sophisticated. But Barracuda costs a fraction of the price and bundles archiving and encryption that Proofpoint charges extra for. Different markets, different value propositions.
Against Cisco Secure Email, Proofpoint has a more modern architecture and better BEC detection. Cisco counters with Talos threat intelligence (which is comparable in some areas) and ecosystem value for Cisco-heavy environments. For email-specific security, Proofpoint leads. For organizations deep in the Cisco stack, Cisco Secure Email may offer better total value.
Against SpamTitan, there is no meaningful comparison. SpamTitan serves SMBs at $1/user/month. Proofpoint serves enterprises at $5-15/user/month. Different products for different markets.
Who Should Use Proofpoint?
Proofpoint is the right choice for:
- Large enterprises (1,000+ users) with dedicated security teams and significant threat exposure
- Regulated industries (finance, healthcare, government, critical infrastructure) where email threats carry outsized risk
- Organizations facing targeted attacks — BEC, supply chain compromise, state-sponsored threats
- CISOs who need actionable threat intelligence for board reporting and strategic security planning
Proofpoint is probably not the right choice for:
- Small or mid-sized businesses without dedicated security staff or budget
- Organizations with simple threat profiles that can be adequately addressed by less expensive solutions
- Companies looking for a set-and-forget email filter — Proofpoint requires ongoing attention
The Bottom Line
Proofpoint is the email security platform that CISOs choose when the stakes are highest. Its threat intelligence is deeper, its BEC detection is sharper, and its people-centric approach is more strategic than any competitor. The price reflects the value, and for enterprises where a single successful attack could cost millions, the investment is defensible.
For everyone else, there are excellent alternatives that deliver strong protection at a fraction of the cost. Email security is not a one-size-fits-all market, and Proofpoint’s strength is knowing exactly which size it fits best.
Related Comparisons
Looking for more options? Check out our detailed comparison pages:
- Proofpoint vs Mimecast — The enterprise email security showdown
- Proofpoint vs Barracuda — Enterprise leader versus mid-market contender
- Proofpoint vs Cisco Secure Email — Threat intelligence heavyweights
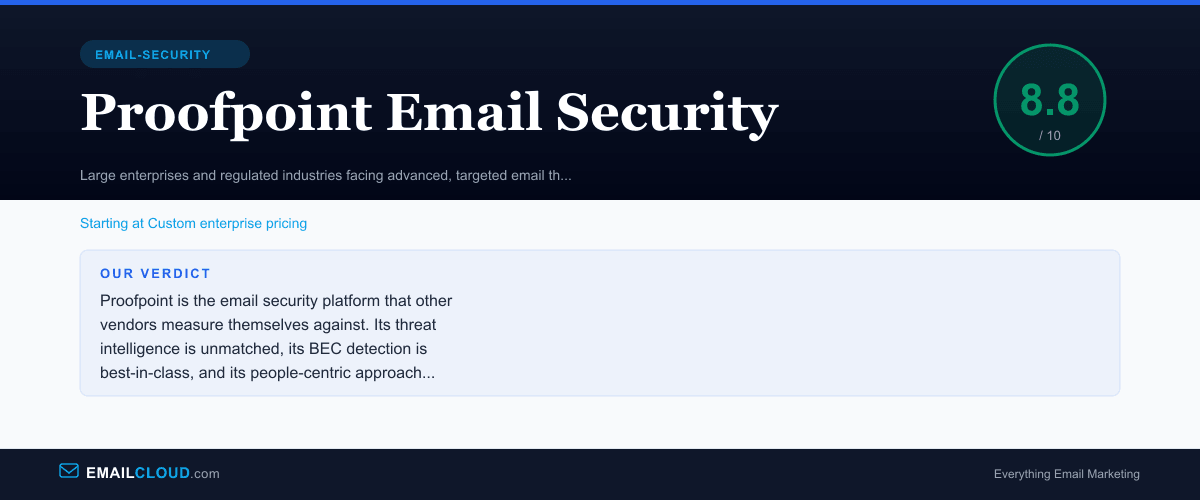
Our Verdict
Proofpoint is the email security platform that other vendors measure themselves against. Its threat intelligence is unmatched, its BEC detection is best-in-class, and its people-centric approach to security represents genuinely innovative thinking. The platform has earned its position as the default choice for Fortune 500 companies and regulated enterprises. The trade-offs are real — enterprise pricing, deployment complexity, and the need for dedicated administration — but for organizations where email is a primary attack vector and the stakes are high, Proofpoint delivers protection that justifies the investment.
Review Summary
Share this visual summary. Right-click to save.
Frequently Asked Questions
Is Proofpoint worth the price?
For large enterprises facing sophisticated threats like business email compromise, supply chain attacks, and targeted phishing, Proofpoint's threat intelligence and detection capabilities justify the premium. The platform consistently outperforms competitors in independent testing against advanced threats. However, for small or mid-sized businesses with less complex threat profiles, the cost is hard to justify when platforms like SpamTitan deliver excellent protection at a fraction of the price.
What is Proofpoint TAP?
Targeted Attack Protection (TAP) is Proofpoint's advanced threat analysis engine. It uses sandboxing, URL rewriting, and predictive analysis to detect and block targeted email attacks before they reach users. TAP rewrites URLs in emails so that every click is analyzed in real time against current threat intelligence. It also sandboxes suspicious attachments to detect zero-day malware. TAP is widely regarded as one of the most effective advanced threat protection technologies available.
How does Proofpoint compare to Mimecast?
Proofpoint and Mimecast are the two most frequently compared enterprise email security platforms. Proofpoint has stronger threat intelligence and more sophisticated BEC detection. Mimecast offers email continuity (keeping email flowing during outages) and built-in security awareness training. Proofpoint is generally considered the better pure security platform, while Mimecast provides a broader operational resilience story. Pricing is comparable, with both requiring custom enterprise quotes.